The scp command in Unix is used to copy files securely between remote hosts without establishing an FTP session or even logging in to the remote system. To transfer data, the SCP command syntax uses SSH, so authentication is required. The files and passwords exchanged with the SCP command in Linux are encrypted, so anyone snooping on the network cannot view them. This is unlike rcp or FTP, and this article seeks to show you how to use the SCP command in Linux.
Files transmitted between Unix or Linux systems can be encrypted with the SCP Command in Linux (Secure Copy). Cp is a safer alternative to copy (copy). Encrypted connections are established over SSH (Secure Shell) using the SCP command, The data is still protected, even if it is intercepted with SCP syntax. Keep reading to see how to use SCP.
SCP Syntax Command
The CLI environment should be familiar to SCP Linux administrators. The GUI mode is not commonly found on Linux servers, and Linux administrators may find SSH the most convenient method to remotely manage servers and not the SCP usage.
In addition to SSH, SCP is also built-in. A secure copy of a file between two servers can be accomplished with SCP. File and directory copies between two locations can be made using SCP (secure copy), a command-line utility. SCP allows for the following operations:
- To remote systems from your local system.
- To local systems from remote ones.
- Your local system and two remote systems.
When processing an SCP command to transfer a file, both the files and the passwords are encrypted to prevent snoopers from getting sensitive information. CLI experience is highly recommended for Linux administrators, and it is uncommon to find GUI modes for Linux servers. Linux administrators may find that SSH is the most popular method for managing servers via a remote, secure connection. SCP commands are built into SSH.
Also Read: 11 Tips to Make Your Dedicated Server More Secure
Getting Started
| scp-v | It sends debugging messages about the progress of scp and ssh. This helps track down problems with connections, authentication, and configuration. |
| scp –s | To use an encrypted connection, you must use the following program. You must know how to use ssh(1) options. |
| scp –p | Accurately preserves file access times, modification times, and modes. |
| scp –q | It turns off the progress indicator. |
| scp –P | Determines the port on the remote server to use. |
| scp –r | It copies an entire directory recursively. |
| ~/ | It stands for the user or home directory |
| * | Specify a string of text |
We’ll first review the basic scp example syntax for the scp command before learning how to use it. The syntax for the scp command is as follows:
“scp [OPTION] [user@]SRC_HOST:]file1 [user@]DEST_HOST:]file2”In this scp command in Linux example, the ‘Option’ field, you need to add any known scp syntax, such as ssh configuration, cipher, ssh port, recursive copy, limit, etc. The ‘[user@]SRC_HOST:]file1’ refers to the source file, and the other ‘[user@]DEST_HOST:]file2’ refers to the destination file.
The path to local files should be specified as a relative or absolute path, but the host and user should be specified for remote files. This SCP command example offers many options for adjusting the program’s behavior, and these are the most commonly used. They are listed in the table above.
The SCP command needs an SSH key or password for authentication on the remote system to transfer data over ‘SSH.’ Using a colon (:) distinguishes local from remote locations in SCP. The source file and target system must allow reading and writing on the same level for you to be able to copy files.
Make sure you don’t copy files that have the same name and location on both systems because SCP overwrites files without warning. The SCP command in Ubuntu should be run within a screen or tmux session to transfer large files.
Recommended: 14 Tar Command in Linux
File copy command
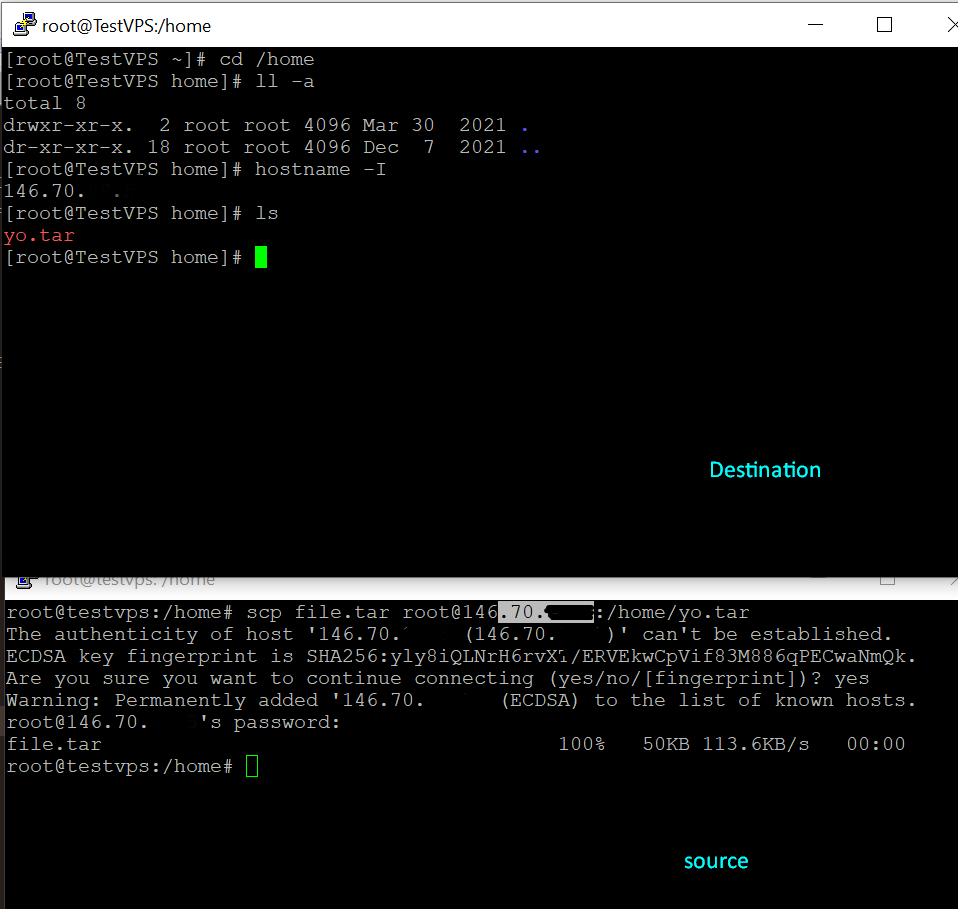
The scp command’s main function is to copy local files to the remote system. The following scp command Linux to copy file can be used to move a file from a local to the remote system:
“scp file.txt [email protected]:/remote/directory”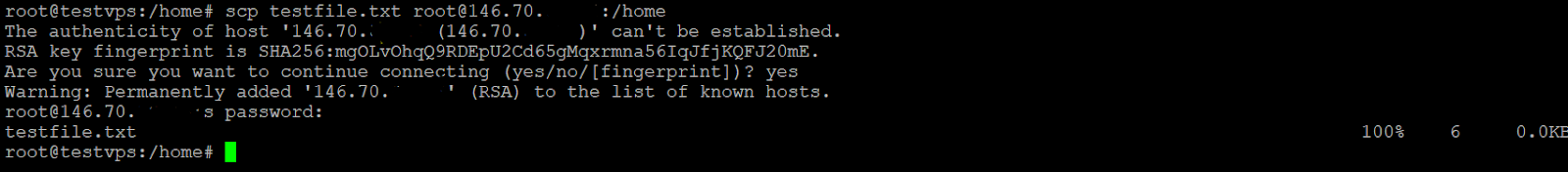
This command copies a file named ‘file.txt’ from one server to another, identifies a user on the remote server by ‘remote_username,’ and sets the server’s IP address to ‘10.10.0.2’. A path to the destination directory is provided by ‘/remote/directory’. You will copy the file to the remote user’s home directory if no remote directory or SCP command Linux folder is specified. The transfer process will begin after you enter the user password.
Using a remote location as a source and a local location as the destination, one can copy a file from a remote system to a local system. You can run the following command at 10.10.0.2 to copy a file named file.txt from a remote server:
“scp [email protected]:/remote/file.txt /local/directory”Altering file names
When the destination location does not contain the filename, the copied file will have the original name. It is necessary to specify the new file name if you want to save the file under another name:
“scp file.txt [email protected]:/remote/directory/newfilename.txt”
As with copying files, a directory can be copied via the same command. Recursive will require the ‘-r ‘ flag. Use the ‘-r ‘ option to copy a directory from a local system to a remote one:
“scp -r /local/directory [email protected]:/remote/directory”Getting SCP process information
By default, the SCP command does not require parameters. There will not be any visible results until the process has been completed or an error has occurred. The “-v” option can be used to display debug information. Debugging problems with connections, authentication, and configuration can be done by using this option.
“username@destination ~/Documents $ scp -v Label.pdf local@@202.x.x.x:.”If you need help with this, you can use the “-p” parameter. The computer will display the estimated time and the speed of the connection. The original files are shown along with modification times, access times, and modes.
“username@destination ~/Documents $ scp -p Label.pdf local@@202.x.x.x:.”Speeding up file transfer
The “-C” parameter can help to speed up your SCP file transfer; your files will be compressed in transit using this parameter. This is unique because compression takes place only over the network, and the file will be restored to its original size once it has reached the destination server.
“username@destination ~/Documents $ scp -pv messages.log [email protected]:.”Encrypting files
SCP encrypts files using “AES-128” by default. For encrypting it, you can change the cipher using the “-c” parameter. Below is an example.
“#scp -c 3des Label.pdf [email protected]:.”Controlling bandwidth usage
Alternatively, you could use the “-l” parameter. The “-l” parameter limits the number of bytes transferred. You will find it helpful if you are automated scripting a more significant number of files but don’t want to use SCP to drain bandwidth.
“# scp -l 400 Label.pdf [email protected]:.”The “-l” parameter’s value of 400 represents a bandwidth limit of 50 KB/sec for the SCP process. Broadband is designated in Kilobytes per second (kbps), and eight bits are the same as one byte, unlike SCP, which counts in Kilobytes per second. This will be useful if you are automating files but don’t want to drain bandwidth with SCP.
Also Read: Steps to Unzip / Extract tar.gz Files in Linux Using Command Line
Summing Up
The purpose of this guide was to teach you what the SCP command-line in Linux is and how you can use it to transmit a SCP file securely. An alternative to FTP, which by default is inherently insecure, is advantageous. Now that you know what the Linux command scp is mainly used to do, get to exploring. A seamless command set is created for managing files between Linux machines with secure copy, supporting regular command line and SSH functionality.